Linux Kernel networking vulnerability allowing potential DoS

A severe vulnerability in the Linux and Unix networking stack has been identified in the last few days. The vulnerability described in CVE-2018–5390 (for Linux) and CVE-2018-6922 (for FreeBSD) allows a potential risk of relatively easy exploitable denial of service attack on an affected machine. The main source of the concern is the wide spread of this issue including plenty of Linux distributions, FreeBSD and some proprietary network equipment operating systems all running the affected Linux Kernels 4.9+ or having the networking code back ported.
The vulnerability is not a complex one. Introduced in Linux Kernel 4.9, it is related to the algorithm that processes the “out of order packages” in TCP connections. That algorithm is responsible to allow the receiving and rearrangement of TCP packets with non sequential numbers in the case of network issues. The problem with the algorithm which brings the potential vulnerability is that it is very resource expensive. According to the report and the calculations just a few thousand out of order packets even from the same source are enough to cause denial of service.
The good news is that some of the most widely spread server distros might not be affected and also the vulnerability still doesn’t have a proof-of-concept exploit So although it’s reported as a severe, this is still not a global issue and patches are already available.
The list of the affected, unaffected and patched distributions constantly updates:
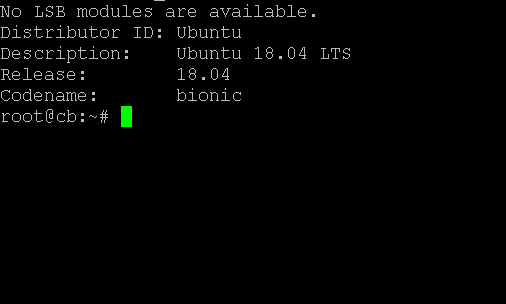
Ubuntu 16.04 and older – Unaffected – Kernel 4.4 is before affected 4.9+
Ubuntu 18.04 – Affected – Patch available through APT
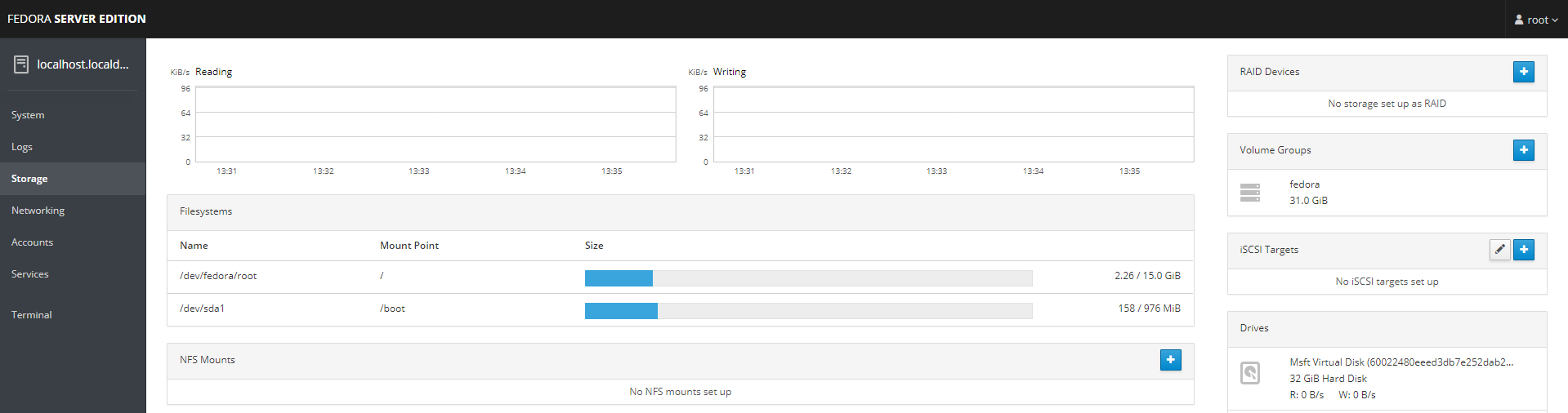
Fedora- Affected
FreeBSD – Affected
OpenSUSE – Unconfirmed
CentOS – Unconfirmed